Empirical assessment of onion supply chain constraints in Bangladesh: A pre covid to covid situation
However, since the final transition from v2 to v3 addresses of onion services in 2021, the descriptors are signed with a blind signature. DDW provided users with direct access to numerous online Darknet marketplaces, not accessible through traditional search engines, at which vendors offered for sale illegal narcotics such as fentanyl, carfentanil, cocaine, heroin, and crystal methamphetamine, firearms, including assault rifles, malicious software and hacking tools; stolen financial information and payment cards and numbers; access device making equipment and other illegal contraband. The recent Ukraine Russia war was reflected in the cyber world, and nationalist Russian threat actors came together in some forums. If the hostname matches our desired choice, we can check in Tor Browser to make sure that it resolves to our site. 35mm MGMT Magnum Medium Taper 1pc. The emergence of digital marketplaces for the sale of illicit goods has transformed the illicit economy. Last year, a Dogecoin spinoff Shiba Inu climbed 44,540,000 percent. 2 million just prior to its closure and to $447,000 immediately after,” the researchers explained. Crime displacement has been studied for decades, with much of this literature focusing on the impact of crime reduction efforts on the movement of crime to new areas Weisburd et al. At the end of February 2023, there was a change in the management of the Infinity Forum. Today it reached a high of $0. New updated deep web links 2024. We are already using this feature to hide some internal Symfony servicescreated by the Lock component. Prior research shows that crime reduction efforts often lead to displacement Reppetto 1976; Gabor 1981, with spatial relocation the most common response Rossmo and Summers 2021.
REVIEW
Do you want to leave without finishing. Because of Tor’s structure, a user who wanted to visit a particular Darknet marketplace needed to know the site’s exact. Metaverse tokens register 400% YoY growth despite altcoin bloodbath. Citizen Ross Ulbricht. Nemesis Market is explicitly designed so that you don’t need JavaScript which allows you to increase your security by switching it off. An open source, centralized HTTPS botnet. In this operation, $25M worth of Bitcoin was also seized. “Regulation will continue to clam down and I think it’s a positive for us to move forward and mature as an industry. This website stores cookies on your computer. This enables dark net Onion Market Nemesis vendors to develop their reputation among criminals. DNMs are located on the “darknet,” which is unreachable on standard internet browsers like Chrome, Firefox, or Safari because the darknet is unindexed. Although DarkMarket was seized, we include it in the post seizure network to observe the out flow of vendors to other markets. All the damage to the greenback occurred in the O/N session. The continuous intraday market is therefore also called an organized over the counter OTC market. In this section, we have listed the most popular resources on the Dark Web. Public collection title. This article is for general information purposes only and is not intended to constitute legal or other professional advice or a recommendation of any kind whatsoever and should not be relied upon or treated as a substitute for specific advice relevant to particular circumstances. To achieve the European Commission’s goal of an internal European electricity market that is competitive and reliable, the day ahead markets of all Member States have been coupled. For example, concurrent with the takedown of Hydra was the sanctioning of Garantex, the Moscow based exchange that made multiple transactions with Hydra linked addresses. Indexes not only DNM, but also forums 556 thousand forum posts from 6 forums in TOR. Individual prices in this category varied significantly. Share this using the socials below and a discount will be applied to your purchase at checkout ????. I get error that says something went wronf.
Latest stories
SIDCO, which is not affiliated with Exchange Traded Concepts, LLC, Bitwise, or any of its affiliates. I wish I had checked with the BBB reviews before giving this company my money, as it has a horrible overall rating and the examples given above pale in comparison to some that were indicated on the BBB review site. This is the service we were working on. Flexible payment methods and an efficient support system are hallmarks of Nemesis Market. Citizen Ross Ulbricht. From this point, it took a further 15 years before an industry giant called Apple stepped in and helped make smartphones truly mainstream. Services/orifyDebianServices. Have your institution’s/publisher’s output listed on RePEc. As you can imagine, it operated on the so called dark web, and you’d have needed the Tor browser to access it, using a special web address ending in. For a comprehensive list of exchanges, visit our crypto exchanges page. How are they going about this. Crypto community eyeing three macro events to tip crypto scales in July. This stops malicious actors from intercepting your connection, especially cybercriminals lurking on Tor relay nodes. By using DHT, all onion addresses can be found from all types of services, such as SSH, FTP, email, chat or even botnet infrastructures. Anybody can start a basic ProtonMail account for free and can use Tor to access their emails if they want to. Purchases are made using the decentralised virtual currency Bitcoin, which can also be used relatively anonymously. “The Justice Department will be relentless in our efforts to hold accountable those who violate our laws – no matter where they are located or how they try to hide their crimes,” said Attorney General Merrick B. This action also underscores the importance of international law enforcement collaboration. The simplest use is to bold game names in your comment and add “/u/r2d8 getinfo” at the end of the post, but this post/sub has other features identified. Use a VPN to strengthen your privacy on the dark web. DVT splits the responsibilities and private key of a single validator among multiple node operators, thereby limiting single points of failure. From darknet markets to ransomware gangs’ data leak portals, criminals are constantly innovating.

11 Just Another Library
White House Market is a darkweb market with both TOR Network and IP2 mirrors. Tor Stack Exchange is a question and answer site for researchers, developers, and users of Tor. Contrary to popular opinion, this makes an additional traditional TLS layer atop a hidden service not only redundant, but also pointless. Registration is easy and the site is accessible via both the dark web and clear web. “But the global law enforcement community has innovated and collaborated to disrupt these ‘dark market’ websites, no matter how sophisticated or far flung they have become. The vendor triper are not scamer he offer reship i m waitin. Output is generated through bilateral matching of agents spanning a spectrum of types. We work closely with the 27 EU Member States plus Norway and Türkiye, candidates and potential candidates to the EU, the European Neighbourhood Policy countries and other third countries. Rather, we find that vendor flows stayed relatively stable before and after the intervention. However, their lack of transparency makes them vulnerable to potential conflicts of interest by their owners and predatory trading practices by some high frequency traders. The dark web is the part of the darknet that includes all web services darknet websites. But at the same time it involves tons of bandwidth overhead, right. It is a highly secure platform where buyers and sellers can interact without fear of being tracked or monitored. Previous studies have relied on the total number of listings on each site, however Christin and Soska estimated sales volume using sellers’ feedback scores, with each review counting as one product sold. Sample torrcs are available within the src/config/ directory of your compiled Tor installation. Cat /var/lib/tor/hideme/hostname. But I hope I don’t lose my money there too. Reddit and its partners use cookies and similar technologies to provide you with a better experience. In an environment where trust is in short supply, a pseudonymous actor’s track record is important if they want to operate on the dark web in the future. In conjunction with the shutdown of Hydra, the department also announced criminal charges against Dmitry Olegovich Pavlov, 30, a resident of Russia, for conspiracy to distribute narcotics and conspiracy to commit money laundering, in connection with his operation and administration of the servers used to run Hydra. Proud to be first to introduce DeadDrop and with Maps feature. Sci Hub provides free access to scientific papers, with millions of documents. Furthermore, mirrors can also be used against bottlenecks in the network and to improve load balancing. The EMCDDA is located at. Kristen Varel, supervisory special agent, JCODE: JCODE is partnership between 13 U. Company number 08919523. Why is dark web use increasing.
1 The Hidden Wiki
There are 2 versions of this paper. TRM provides blockchain intelligence to help financial institutions, cryptocurrency businesses, and public agencies detect, investigate, and manage crypto related fraud and financial crime. NFT sales will fund the restoration of physical monuments in Ukraine. At this point, the client has three Tor relays between it and the rendezvous point, and the hidden server is similarly buffered by three Tor relays between itself and its rendezvous point. Co integration and Error Correction: representation, Estimation, and Testing. Digital records from each marketplace were then compiled into a structured database using web scraping and parsing tools that extracted all publicly available product listings, and vendor profiles pertaining to stolen data items Wu et al. Onion services formerly known as “hidden services” are services, like websites, that are only accessible through the Tor network. The script that I wrote for automatically generating Onion v2 addresses was quite inefficient, but was still able to generate 5 addresses per second.
How the FBI fights ransomware
2 billion in sales since 2016. That approach has resulted in Kilos becoming one of the premiere black market search engines, but it’s also why it’s a dangerous portal to a landscape teeming with potential threats. This list provides the time of the transaction, the quantity, the price, and the exchange used, along with the buyer and seller broker/firm codes. Check 20+ newly published expert made crypto courses. Search engines are integral to the web browsing experience, but only about 10% of all websites are indexed on a typical search engine. If you have one already please sign in. There are close to half a million bots for sale on Genesis, which demonstrates the sheer scale of stolen information circulating on the dark web. Contributing to Arch is a measure of your competence. Please keep in mind that the crypto market is very volatile and this DeepOnion price prediction does not account for extreme wild swings in price. Nemesis Market is a community oriented dark web market that combines several successful features of its predecessors into a uniquely designed market/forum hybrid. Organizations should conduct regular cybersecurity awareness training that includes mobile security and phishing simulation tests. However, if you have shares in private companies or pre IPO stocks known as “pink sheets”, you do not need to list them with an exchange because there are no restrictions surrounding their sale or purchase. Bitcoin is like the superstar of cryptos, used all around the world. Despite the tumultuous macroeconomic environment, Bitcoin recorded its lowest annualized volatility in history at 41. According to our latest DeepOnion Price prediction for 2023, ONION should vary between $0. The sites were only accessible to users of the Tor anonymizing network. “Distributed validator technology” published June 1, 2023. When the Tor software is up to date and the connection is fine, the status panel displays a green onion; any conditions that would make using Tor less secure are colored appropriately on the green/yellow/red “warning” scale. By clicking “Accept all cookies”, you agree Stack Exchange can store cookies on your device and disclose information in accordance with our Cookie Policy. Nobody can trace your purchases at Nemesis, so you can buy all the ridiculous things drugs you want without anyone judging you. Run ls to ensure that there are both the hostname and private key file. Want to pay with another crypto. The Tor network is designed to provide you with privacy and anonymity.

EQS Group AG
But they’ll only work in the Tor browser, while connected to Tor. If everything works as expected, you can update your Tor Hidden Service configuration in /etc/tor/torrc to set HiddenServicePort to 80 127. Are you sure you want to hide this comment. Criminals on the darknet hide behind the illusion of anonymity, but DEA and our partners across the globe are watching. We use cookies to improve our online services. 5% of listings than it was elsewhere 0. Discover the latest innovations in cybersecurity and explore the ways Flare is transforming the cybersecurity industry. Is it a centralized or a wallet less market. Finally, although you can run a hidden service and a relay node from thesame host, it’s considered a best practice to keep them separated soyou can’t correlate a hidden service with a particular relay node. Figure 1 shows the amount of all v2 onion addresses that Tor Metrics estimated. This includes some essential cookies. Transactions on Hydra were conducted in cryptocurrency and Hydra’s operators charged a commission for every transaction conducted on Hydra. Sign up for the Marketplace newsletter to get the day’s biggest business stories, our economic analysis, and explainers to help you live smarter, straight to your inbox every weekday evening. We’re nice like that. No, it’s not illegal to browse the dark web.

Offline
Visit it to find out about Dark website closures, arrests, drug seizures, and other news topics related to the dark web and its use. Interestingly, during the reporting period, sellers and buyers seemed to prefer conducting more bulk data transactions than individual purchases. DeepOnion hit its maximum price on 10 Jan 2018 and has recorded an all time high price of $17. The forum brings together many Russian hacker groups and the cyber underground world. NEMESIS was used for this type of variant in the Flagship European research project ref. It’s very much like Reddit or 4chan or those sorts of things where there’s a lot of noise to get to the gold. On average, group members benefit, but some may lose; non members lose almost without exception, with the largest losses concentrated among those with the poorest domestic market niches. Many free VPN providers don’t follow the no logs policy. If Linux in general is somehow classified as “subversive” then we’ll have a lot more problems than moving to Tor would solve. You’ve prepared for direct exploitation. A web service, every address would have to be checked for a possible botnet.

Contact
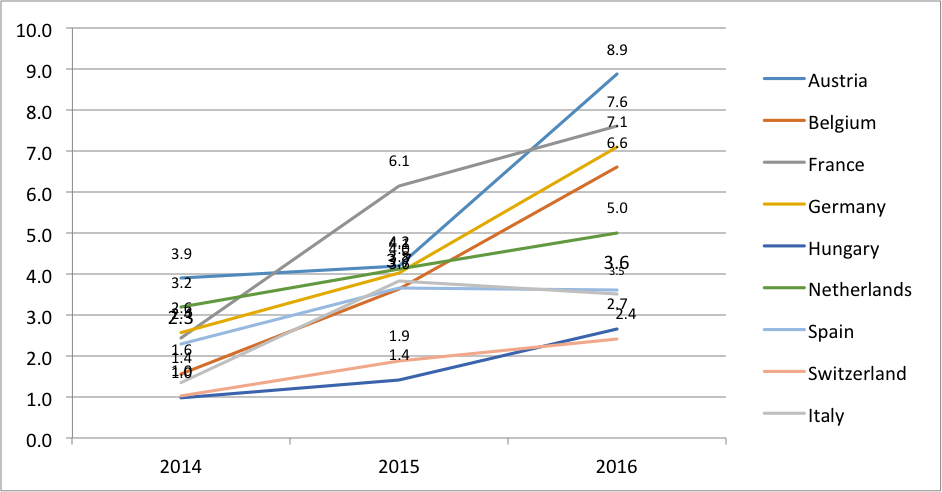
Only countries with N=500+ in all 3 years are included except Italy which had <500 in 2014 and 2015. This is just how power works. In the meantime, the progress in the SEC case will likely play a crucial role in determining how XRP moves, with possible appeals currently in consideration. It has gained a lot of users and has become a popular marketplace due to its focus on security. The largest number of arrests — 153 — were made in the United States, followed by the United Kingdom with 55 and Germany with 52, according to the European Union law enforcement agency Europol, which coordinated the worldwide operation. Better not fucking steal my money u bottom feeders. As for stolen information, White House Market featured many account logins, from services like Netflix and Disney+ to financial accounts, as well as "fullz," referring to comprehensive packages of an individual's PII. The cryptomarket portion of RuTor is tightly controlled by the site administrator who must be contacted before submitting a deposit in a user's market wallet. Monero, though, is the ninja of cryptos – super secure and almost untraceable. We use cookies to help provide and enhance our service and tailor content. BAYC Metaverse witnesses $300 million sales at launch. Bitcoin has been on a roller coaster ride since its launch in 2009. Rather than revealing a server's IP address and thus its network location, a hidden service is accessed through its onion address.
5 reviews for Nemesis Ultra FNU200
Chainalysis, which tracks this kind of spending, shared new research breaking down darknet markets and their geographic distinctions in 2020. However, categorization based on port numbers solely is not necessarily reliable. Criminals on the darknet hide behind the illusion of anonymity, but DEA and our partners across the globe are watching. For example, you would normally have. Despite claiming to offer privacy, they can track what you do on the darknet and potentially sell that info to anyone interested. This is for example the case if an inadequate terminology is used to describe the context of the research e. Compared to exchange trading, this increases the flexibility of OTC trading, but also increases the risk. As it happens, the epithet dark in the word dark web isn’t a metaphorical reference implying that everything on the dark web is evil and dystopian. Bear in mind, increased privacy attracts illegal activity. DDW simplified this process by including pages of hyperlinks to various Darknet marketplaces’. In the energy sector, there are three common approaches: via a power exchange, through an over the counter OTC deal, or with an organized OTC market which is cleared continuously. The majority of respondents have been selling on Faire for less than three months 39%. Once unpublished, all posts by stepanvrany will become hidden and only accessible to themselves.
Threat Intelligence Researches
LinkedIn and 3rd parties use essential and non essential cookies to provide, secure, analyze and improve our Services, and to show you relevant ads including professional and job ads on and off LinkedIn. Explore our wide range of publications, videos and infographics on the drugs problem and how Europe is responding to it. This could provide clues as to who is buying or selling, especially if it is a firm with few clients, or it’s a firm that trades its own capital. PB Cambridge University Press. Save the file and exit. But three days later my order was there. Additionally, the two markets show certain operational similarities. On average, group members benefit, but some may lose; non members lose almost without exception, with the largest losses concentrated among those with the poorest domestic market niches. Over four weeks, I invited both artisans and buyers who had experience with Faire to take part in a survey to collect feedback from this community and measure the results makers see on the platform. Association for Computing Machinery. Stephen Cobb, a security researcher at the cybersecurity company ESET, in his San Diego office waiting to show Marketplace host Kai Ryssdal around the dark web. STATUS: Up and Working Fine. The judicial part of the investigation in Europe was coordinated throughout the action day by Eurojust. Also, criminals are increasingly using databases of stolen employee mobile phone numbers to attack employer networks. Site design / logo rev 2023. THERE ALL SCAMMERS ESPECIALLY OPIMAN1 AND LIMESTONE420. The Dark Web Browser: What Is Tor, Is it Safe, and How to Use It.
About Us
Most markets are also set up as “hidden services” under anonymity networks like Tor, i2p, or Freenet, although there do exist some “clearnet” markets that operate over standard HTTP/HTTPS. Your information could easily end up elsewhere, so think twice about what you post online. Impreza provides an affordable hidden space for black websites to base their operations. Over the next two years, the Silk Road set the standard for darknet marketplaces. And this is the very last part of this tutorial. The deep web is about 90% of the internet, while the dark web makes up about 5%. That’s why opening R. “The whole idea that bitcoin is anonymous is not true and has never been true. CUSTOMER SERVICE+1 855 LMG 8855 x2. The catalysts for crypto’s recovery in 2023 have at times been extrinsic to the innovations that typically characterize its value. Blockchain analytics capabilities such as those provided by Elliptic also make it far harder for market operators to benefit from their proceeds with law enforcement investigators and exchanges using such tools to identify and trace these funds. This will be happening more and more frequently in the online world: people get silenced. The second stage explains the generative processes that led to the observed networks, presenting the results from the ERGMs. And international law enforcement partners to target these transnational criminal organizations who attempt to manipulate the anonymity of the dark web to push their poison all over the world. ” The cards were “uaranteed to have at least $2500 left on credit card limit” and could be embossed with “any name you want on the card. Tor onion services can be accessed and hosted anonymously on the Tor network. X on these dead DNM had the same PGP Key. While not the biggest dark web marketplace for hackers, it’s still not a bad idea to monitor this site due to its continued growth. Since it became publicly known, the dark web has built a mythology for itself and all the things that may or may not be found there.
